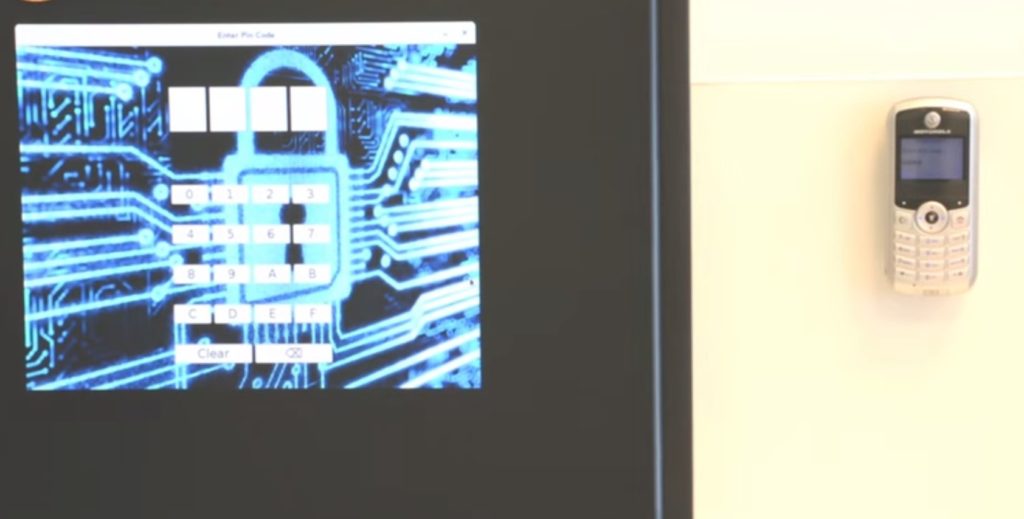
Hacking a Computer with a Simple Cellphone
Hacking a Computer with a Simple Cellphone
July 30, 2015
Wired — The most sensitive work environments, like nuclear power plants, demand the strictest security. When the work is classified or involves sensitive trade secrets, companies often also institute strict rules against bringing smartphones into the workspace, as these could easily be turned into unwitting listening devices.
But, BGU researchers have now devised a new method for stealing data that bypasses all of these protections — using the GSM network, electromagnetic waves and a basic low-end mobile phone.
The researchers are calling the finding a “breakthrough” in extracting data from air-gapped systems. It serves as a warning to defense companies and others that they need to immediately “change their security guidelines and prohibit employees and visitors from bringing devices capable of intercepting RF signals,” says Prof. Yuval Elovici, director of BGU’s Cyber Security Research Center, where the research was done.
The research was conducted by lead researcher BGU Ph.D. student Mordechai Guri, along with Assaf Kachlon, Ofer Hasson, Gabi Kedma, Yisroel Mirsky, supervised by Prof. Yuval Elovici. Guri will present their findings next month at the 24th USENIX Security Symposium in Washington, D.C.
This basic cellphone-based hack builds on a previous attack the academics devised last year using a smartphone to wirelessly extract data from air-gapped computers.
It works with simple feature phones that often are allowed into sensitive environments where smartphones are not, because they have only voice and text-messaging capabilities and presumably can’t be turned into listening devices by spies.
Though the attack permits only a small amount of data to be extracted to a nearby phone, it’s enough to exfiltrate passwords or even encryption keys in a minute or two, depending on the length of the password.